A frequent visitor here will know that we have many articles discussing the netsh command line shell/scripting tool in Windows. The tool was originally introduced in Win2K. If you aren’t a regular – just click on ‘netsh’ in the tag cloud to see them all.
This article discusses how you can use the ‘netsh trace’ function to actually perform a packet capture from the command line in Windows. Technically this means you do not need a capture tool on a Windows machine other than the OS itself.
To analyze and view the packets, you need a tool, and our favorite is Wireshark, of course!
Here is how to use netsh to accomplish this task.
[Note: you may need to use Run as Administrator to get your system to work correctly]
We begin by examining the help screen with the following command:
netsh trace start ?
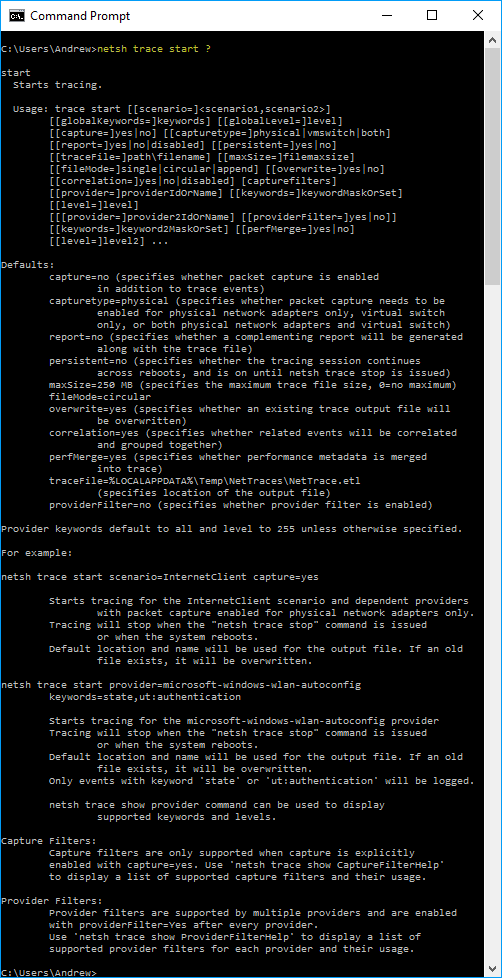
You can see there are many options.
To do a simple trace/capture we will use the following command:
netsh trace start capture=yes traceFile="c:\netsh_trace.cap"
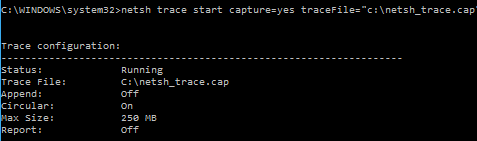
The capture will run in the background.
To stop the capture, use the following command:
netsh trace stop
It will take several minutes to close. Be patient!

If we go and look at my directory c:\ we see the file was saved as follows:

And if we try to open either of them in Wireshark, we get the following error:

So you have to use something like Microsoft Message Analyzer (now retired – see their web page here: https://docs.microsoft.com/en-us/message-analyzer/installing-and-upgrading-message-analyzer ), or the older (now in archive, but still works) Microsoft Network Monitor (https://www.microsoft.com/en-us/download/details.aspx?id=4865) to open the file, and then you will be able to export it so you can analyze in Wireshark.
Comments are welcomed below from registered users. You can also leave comments at our Discord server.
If you would like to see more content and articles like this, please support us by clicking the patron link where you will receive free bonus access to courses and more, or simply buying us a cup of coffee!
