Someone asked the following “getting started” question on the Wireshark Discord site, and it prompted me to write this FAQ to help newcomers to Wireshark understand how to navigate the initial complexity of packet capture.
Hi everyone! I’m new here and just downloaded wireshark for a Computer Comm class. I need to capture traffic sent to a specific website, explain the sequence of events (DNS exchange, ARP, TCP Connection, Web page request, TCP teardown, etc.) and explain what each part does. I’ve run a capture, opened a browser and gone to the website, and then stopped the capture but there is SO MUCH to view in the capture…my head is spinning! Can someone help me understand or point me to an example or a video which could help? Thank you so much!
One response was:
I suggest closing as many apps as possible when doing the experiment otherwise you will see eg. packets between Discord and a dozen different servers getting in the way of what you’re looking for
My response was the following:

Hi. Doing those things are great ideas to try and lessen the confusion, but I personally think its the wrong direction. Let me explain. There are always going to be a lot of packets from lots of various operations and sources/destinations. I am going to keep this simple. The whole approach to clarifying and understanding what is going on using Wireshark is to know how to filter that traffic – it is an essential Wireshark skill. Boiling this to a very simple initial set of steps, I would do the following:
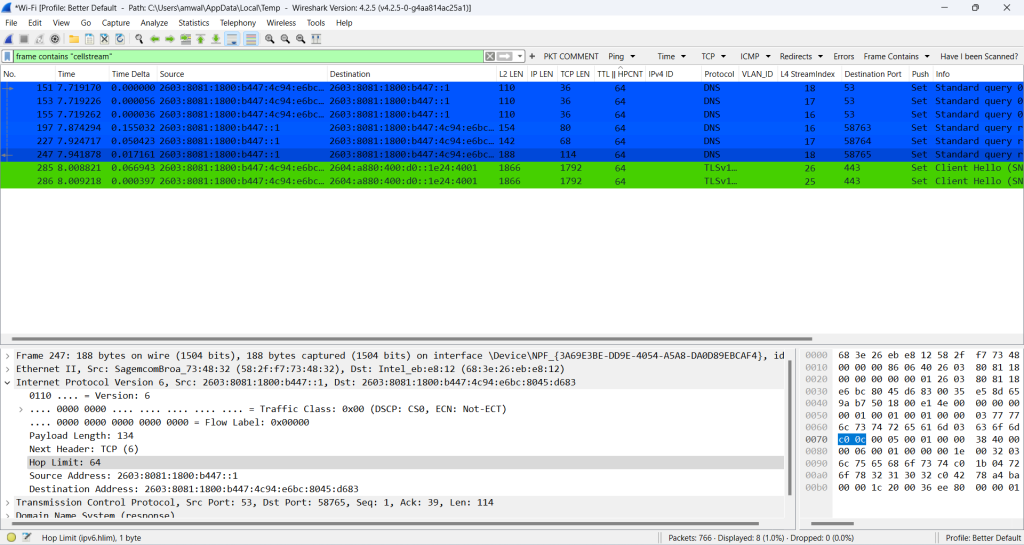
First, use a ‘frame contains’ filter for the URL of the website…for example if you went to facebook.com simply use this filter in the display filter field: “frame contains “facebook””. This will immediately reduce your view to essentially the DNS exchange and possibly some TLS packets. Now you could filter for ‘dns’ packets as well, but that will give you all DNS activity. In my case I used frame contains “cellstream”:
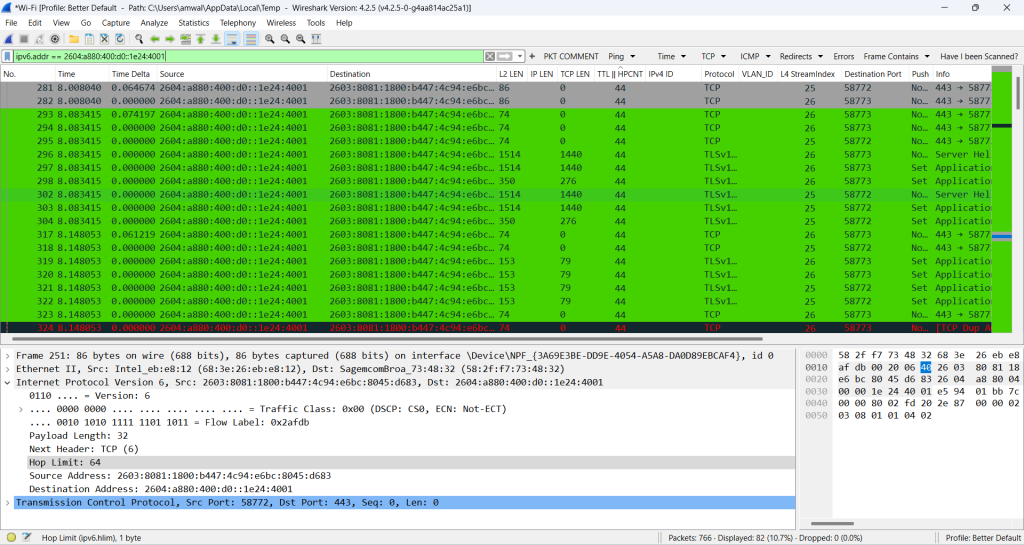
Next, with the DNS packets now in front of you, look for the destination IPv4 or IPv6 address of the web site, and place the following filter in the display filter “ip.addr=={insert the ipv4 address here}” . OK if it is IPv6 then use “ipv6.addr=={the ipv6 address}. Now you will see the TCP conversation with the web server you selected.
I hope this helps set the key point of my response, which is to learn and master the filtering capabilities. Again, for the wizards, I know I over simplified, but hopefully this sets you on a good path.
That simplified, there is a lot to learn about display filtering in Wireshark: see more by clicking on this link: https://www.cellstream.com/?s=display+filter
Comments are welcomed below from registered users. You can also leave comments at our Discord server.
If you would like to see more content and articles like this, please support us by clicking the patron link where you will receive free bonus access to courses and more, or simply buying us a cup of coffee!

