|
Check out these great references as well: |
| Our custom profiles repository for Wireshark |
| Our Udemy course on Wireshark |
| Our Udemy course on Wireless Packet capture |
For those of you who love Wireshark and are asking the question:
How do I find what HTTPS site were visited within a capture?
I have a clever and very usefull answer.
The problem for most users of Wireshark is that Wireshark does follow TCP and other streams really well, but there is an assumption in this method that assumes you have sort of found what you are looking for. Almost everything I see on YouTube illustrates these built in methods, and again this is fine if you know which stream or what you are needing to look at. As one student put it – “they always just seem to know”.
Exactly. What if you don’t? Where do you start?
I think it is really important to get off on the right foot here. Therefore, we begin with our HTTPS profile. Profiles are one of the most important Wireshark capabilities. Setting up and using different profiles for different environments, protocols, and tasks is a crucial skill that we teach in our Wireshark courses. Let’s say you went to the Wireshark site and tried to find some! Suprisingly, here is what you would get:
Whaaaaat?????
No worries. We have an answer below:
Let’s look at what you get with this default basic HTTPS profile.
Capture Filters
Here are the capture filters in this profile:
![]()
Display Filters
Here are the display filters in this profile:
![]()
Colorization:
We have not changed any of the default colors.
Columns
Here are the columns set up we like:

Again, all of this is a great starting point. What do you think we are missing? What would you add? Let us know in the comments below.
Let’s look at how we can leverage this profile.
To learn the power of profiles, check out this video:
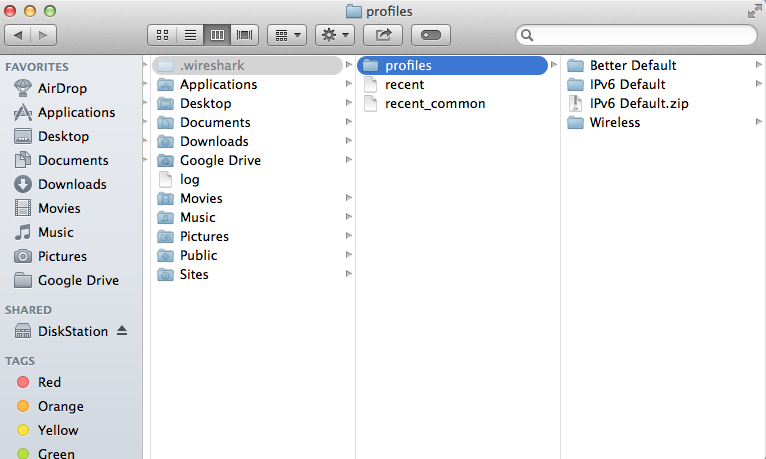
To download this zipped profile click here. Make sure you unzip it into your personal folders, profiles subdirectory as shown in the video:
How Do I use This?
Excellent question.
The first thing to do is make sure the profile is in play. Click on the profile area of the bottom information bar of Wireshark, and select the HTTPS profile.
Next, I apply the display filter called SSL Handshake Servers List.
These are all the packets that contain a HTTPS Client Hello packet via SSL to some server:

We now see what sites have been visited in the Server Name column.
Select one of the packets of interest by clicking on it once (I selected the platform.twitter.com packet):
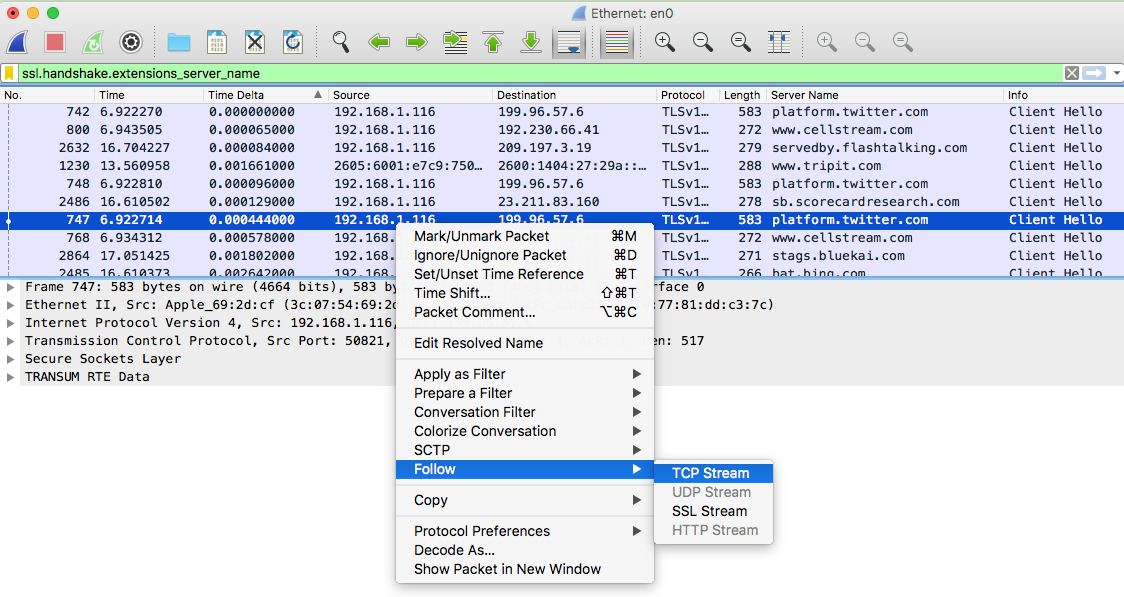
Right click on the packet, select Follow> TCP Stream:
You will get the filtered TCP Stream (note in this case the filter is ‘tcp.stream eq 13’:

Poof – you are there!
We hope this helps you with finding HTTPS sessions and Wireshark! The next question is how to decrypt this information. I have written several articles on decryption:
Got a better way? Or have a profile you would like to send to us? Send it to andyw@cellstream.com – thanks in advance – we share profiles here.
Another way to find profiles, click on “Profile” in the tag cloud at this site.
I hope you find this article and its content helpful. Comments are welcomed below. If you would like to see more articles like this, please support us by clicking the patron link where you will receive free bonus access to courses and more, or simply buying us a cup of coffee!, and all comments are welcome!
