| Check out these additional IPv6 Resources: |
|---|
| Our IPv6 overview course at Udemy |
| Our IPv6 Custom Profiles for Wireshark |
| Our IPv6 classes at the Online School |
I want to continue my articles on IPv6 Security with an example of IPv6 Fragmentation.
That said, one way to possibly bypass any security functions in a router or firewall may be to send fragmented packets through the device. This has been shown to work in defeating RA Guard for example. You can read more about that here.
Now, getting IPv6 packets with any extension headers on them at all to pass across the Internet is darned near impossible. See the RFC that reported these findings here.
So to observe this phenomena, in our IPv6 Security class we use a closed lab system. Then we use an IPv6 attack tool to create the packets and blast them at end user systems/servers/routers to see what happens!
Using Wireshark, here is a brief view of what the attack looks like:
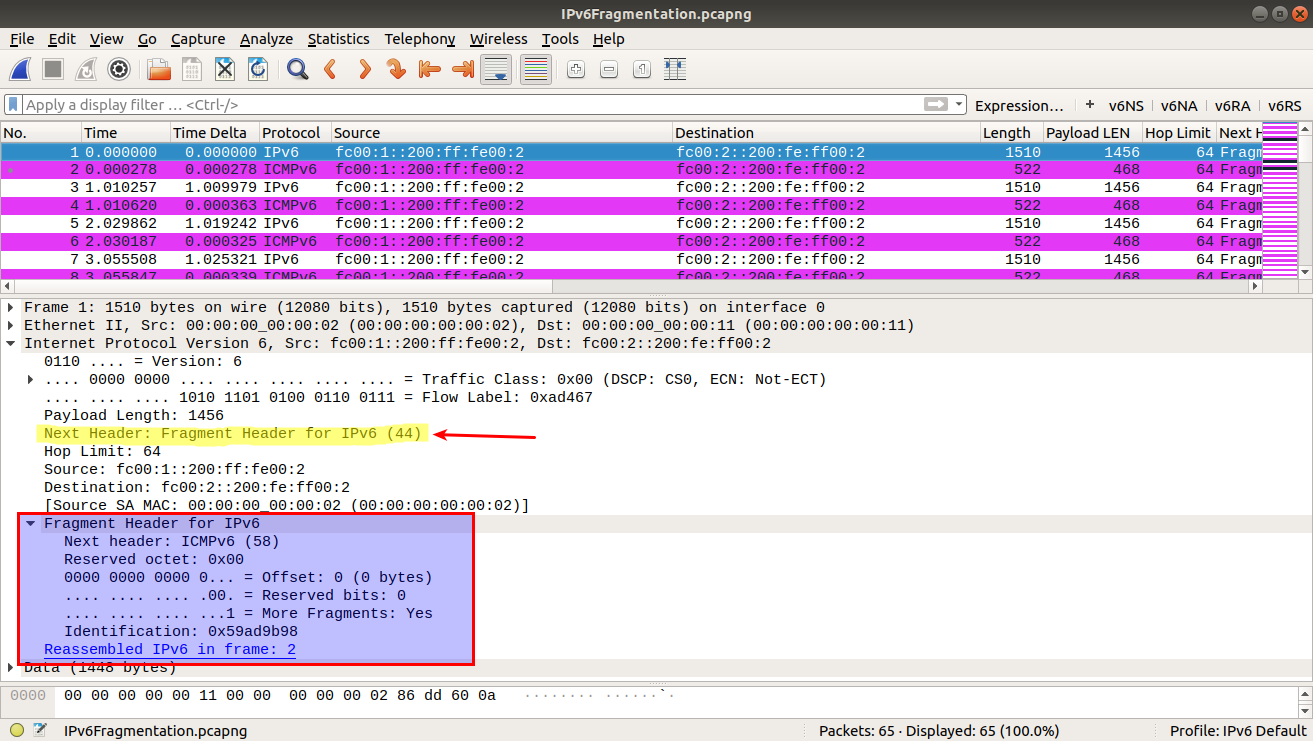
We can see the Fragmentation Extension header indication: Next Header = 44
Then we see the fragmentation header present. What is cool (kudos to Wireshark here), is that as with IPv4 the Wireshark Expert annotates the dissection with an indication/hyperlink to the point of reassembly, and then actually does the reassembly, like the end user station would do, to verify the fragmentation process.
What could this attack do? Well, it depends. It simply could be a throughway past any detection systems. It could consume CPU, leading to a Denial of Service. It could indicate that the network is tossing these type of extension headers, which means we may want to create a more complex packet to get into the network.
You will note we are using our IPv6 default profile – it can be found in our profile repository here.
And, if you would like a copy of this .pcap-ng file for your own self study, you can download it here.
I hope you find this article and its content helpful. Comments are welcomed below. If you would like to see more articles like this, please support us by clicking the patron link where you will receive free bonus access to courses and more, or simply buying us a cup of coffee!, and all comments are welcome!
