Who is on my network? Great question. Better yet: Who is on my customer’s network? That would be looking at the issue from a service provider’s perspective. This article attempts to answer that question with tips and tricks and tools that will help you, whether you are the owner of a network or a service provider. There are multiple ways to attempt to answer this question, and there are several – let’s call them impediments, that may limit our chances for 100% success. I should mention there is another article I have written on this subject – I call this article option 1, and the second article option 2. You can read the option 2 article here. To begin, I will say this: your level of success will depend on where you are. If you are on the network itself, connected, you will have a greater chance of success. Also, if your router provides a list of connected devices, your chances of success will be greater.
Impediments
What could possibly go wrong? The answer is we have several roadblocks to discovering what is on out network that we need to be aware of up front:
- Devices going to sleep: battery operated devices tend to go to sleep and during that sleep they are not easily woken up to made detectable. There may be ways to wake them up, but imagine for a moment a phone or tablet that has been placed in a “do not disturb” state. If it goes to sleep it will be hard to wake up.
- Devices that do not answer to standard protocol prompts: some operating systems and devices won’t respond to some methods of discovery. This means we may need to try multiple methods.
- Some devices may linger in tables and are actually not connected to the network. We will call these false positives for now, but we need to be aware of this possibility.
Starting Point – the Local Router
The huge assumption here is that you have access to the router configuration, and the router operating system provides the information we are looking for. Generally, you will use your web browser and go to your router IP address (e.g. https://192.168.1.1). I cannot do this with my service provider router, but I know they can. If you can get in, look for the DHCP table, or a list of connected devices. Here is an example that I found on the web: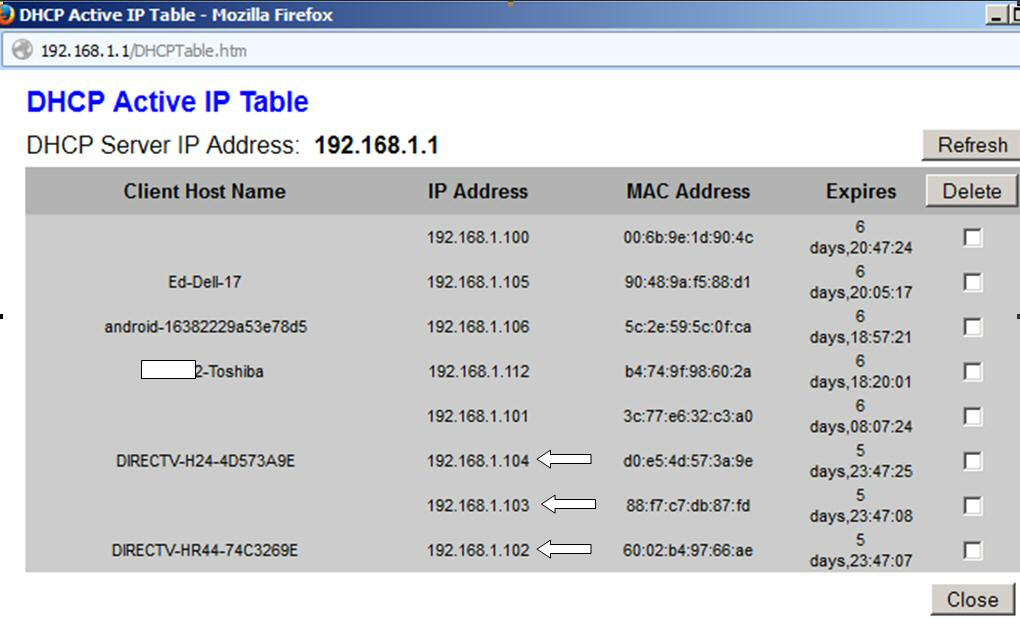 The issue here is that these are kept for days and may not reflect actually what is connected to the network – for example Ed’s Dell may be at work right now. Still there is likely that the DirectTV stuff is indeed there. Now the connected devices tables may be more helpful:
The issue here is that these are kept for days and may not reflect actually what is connected to the network – for example Ed’s Dell may be at work right now. Still there is likely that the DirectTV stuff is indeed there. Now the connected devices tables may be more helpful: So depending on the router and it’s operating system and the ability to view certain pieces of information, this may well be a great way to see what is on a given LAN or WLAN assuming you have access to it.
So depending on the router and it’s operating system and the ability to view certain pieces of information, this may well be a great way to see what is on a given LAN or WLAN assuming you have access to it.
Windows Command Line/Powershell
Here are some commands you can run from the Windows command line.
net view
If you open a command line (Start> Run> type cmd and make sure you run in administrator mode), then enter ‘net view’, after a few moments you will get the following: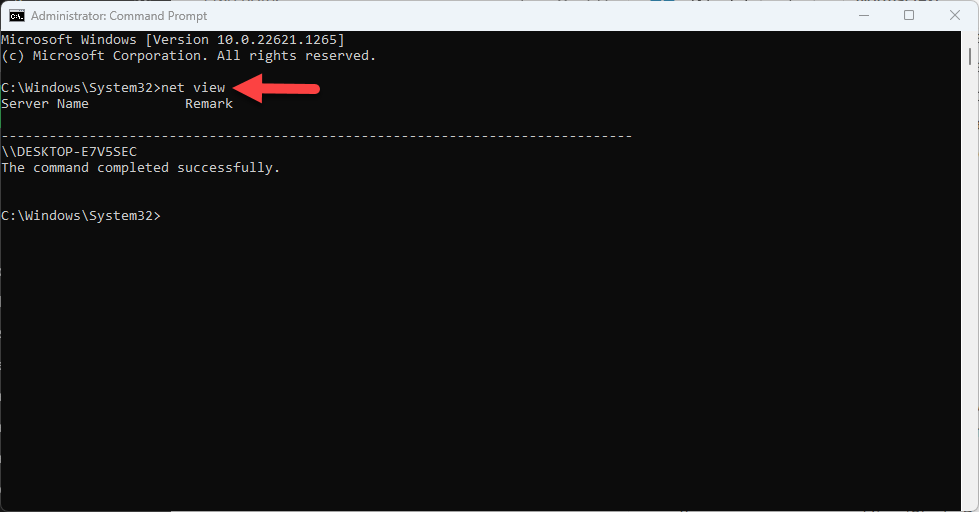 Now, in my case because I am not connected to a domain, I just got my own computer. More specifically, net view returns the computers in the current domain or network. This list will only show computers that have file and printer sharing enabled. There are several options:
Now, in my case because I am not connected to a domain, I just got my own computer. More specifically, net view returns the computers in the current domain or network. This list will only show computers that have file and printer sharing enabled. There are several options:
- net view /all shows all shares available, including administrative shares like C$ and admin$
- net view /domain:yourdomain.com will list all of the sharing computers in the contoso.com domain
- net view /all /domain shows all shares (regular and administrative) in the domain
You can read more on net view here: https://learn.microsoft.com/en-us/previous-versions/windows/it-pro/windows-server-2012-r2-and-2012/hh875576(v=ws.11)Needless to say, I am not a big fan.
arp -a
The arp command is a way to display the ARP cache of your system. It is not a scanner. For this one you do not need to be in administrator mode. Here is an example output that I have annotated: So you see the multiple interfaces and the possible systems that exist in each LAN. Statis ones are generally common addresses like broadcast addresses or multicast addresses that don’t represent a single individual system. So for our purposes, those do not count. The dynamic addresses do represent addresses that have been learned are in my systems ARP cache. The problem with this is we may not see everything depending of how much communication has occurred. For example, this output may be small, then I run a scanner like Colasoft and then re-run this command and all of a sudden I see lots of devices. The arp command can do other stuff, but remember it is not a scan. Here are the command line options:
So you see the multiple interfaces and the possible systems that exist in each LAN. Statis ones are generally common addresses like broadcast addresses or multicast addresses that don’t represent a single individual system. So for our purposes, those do not count. The dynamic addresses do represent addresses that have been learned are in my systems ARP cache. The problem with this is we may not see everything depending of how much communication has occurred. For example, this output may be small, then I run a scanner like Colasoft and then re-run this command and all of a sudden I see lots of devices. The arp command can do other stuff, but remember it is not a scan. Here are the command line options: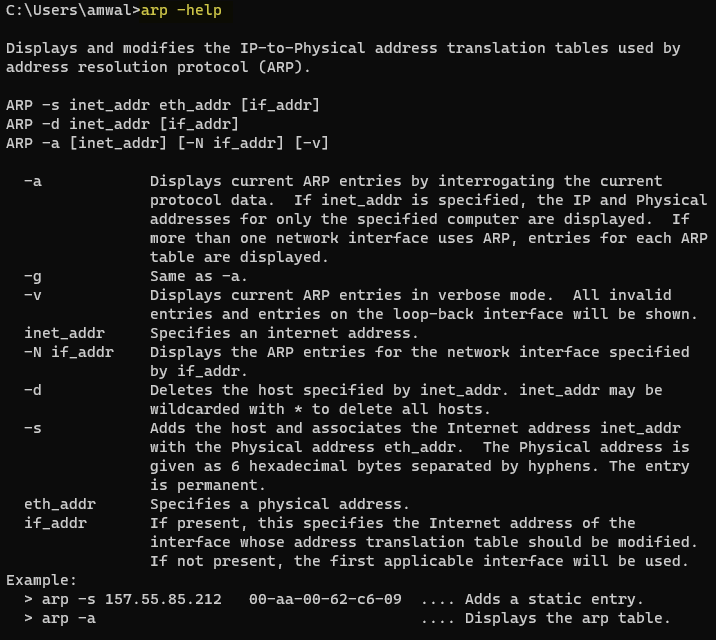 In a pinch, remotely talking to someone, I might try this as every system supports this command.
In a pinch, remotely talking to someone, I might try this as every system supports this command.
nmap
The nmap tool is not installed, but if you were to install it, it is run from the command line. I love nmap as it is a true and very powerful scanner. I have written several articles on nmap, and if you are allowed to use it, use it and learn it. You can find my articles here: https://www.cellstream.com/?s=nmap and I suggest starting with the getting started with nmap article and then graduating to the others.
Linux Command Line
I have always felt that Linux provides more options from the command line than Windows, and I think for discovery the same argument could be made. Let’s look at a few options.
arp-scan
You may have to install this: ‘sudo apt install arp-scan’.Here is an example usage and output: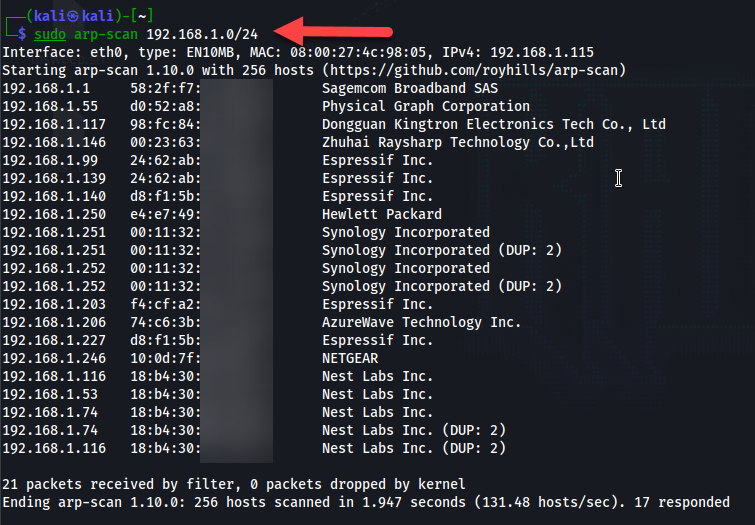 You can also use the arp -a command as in Windows.You can also install and run nmap if it is not already included in your Linux distribution. If anyone has some other Linux tools let me know and I will add them and play with them.
You can also use the arp -a command as in Windows.You can also install and run nmap if it is not already included in your Linux distribution. If anyone has some other Linux tools let me know and I will add them and play with them.
Stand Alone Tools
The following are installable stand alone tools for Windows users that will help.
The Angry IP Scanner
This is a free tool you can download here: https://angryip.org/download/#windows

I like this tool, but I also like the next option.
Advanced IP Scanner
This is a free tool that you can download and install from their web page here: https://www.advanced-ip-scanner.com
I like this tool. Here is a sample output from my network:
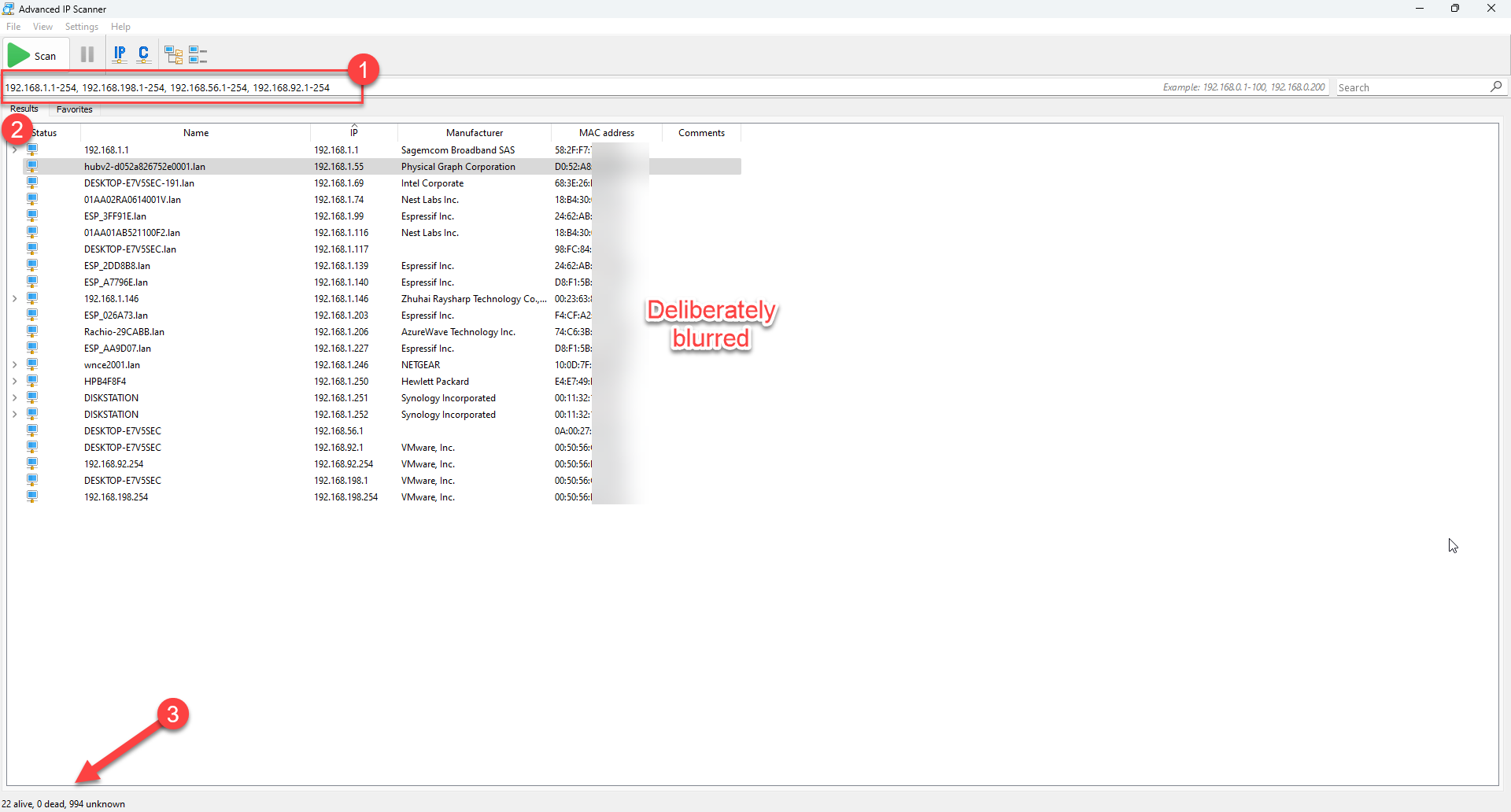
You can see that the scanner has automatically selected networks that appear to exists based on my system interfaces (1). Then as it scans, it outputs systems it has found (2). In the end, when the scan is done it says how many systems are alive. It even finds virtual machines.
There are a couple of interesting options. You will notice that once the scan is done, the program has noticed some common open ports indicated by the > sign next to that IP (1):
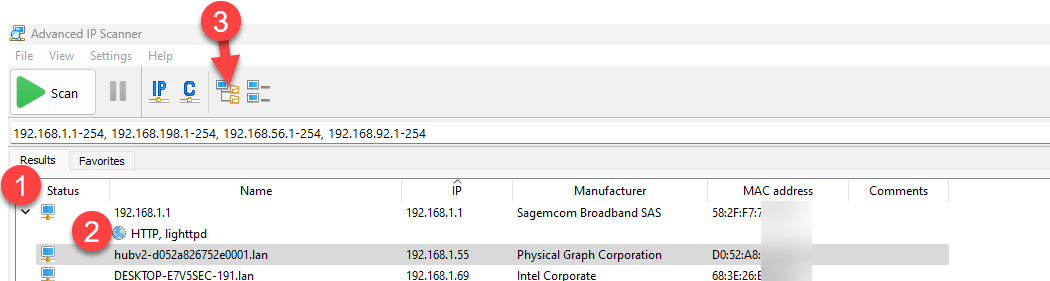
You can click on the expand button (3) or the > sign to expand an individual system information and you will be told what common ports are open (2). Nice. The collapse button is just to the right of the expand button.
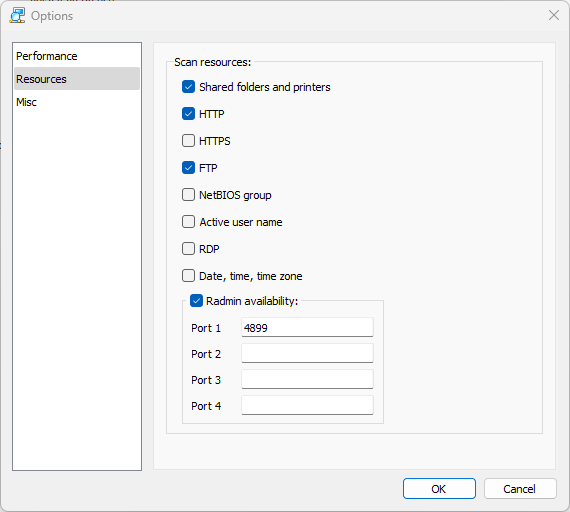
In the program settings, you can check for other common ports as well as add some special ports if you wish:
Further there are more hidden tools when you select a particular device and then right click:
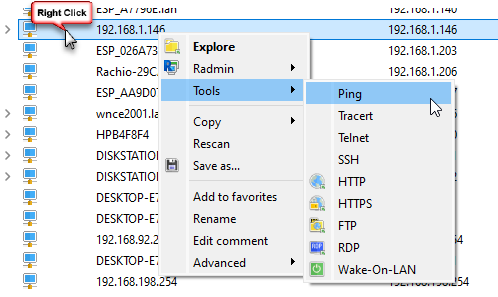
You will see there are tools to further test the system selected. I will not go into all of this here as you can research more on the documentation of the tool. Again, this is a great tool, and I use it.
Colasoft MAC Scanner
Colasoft makes a suite of products, some cost money and some are free. There is a free edition of this tool available for download here: https://www.colasoft.com/mac_scanner/
It is a bit simpler than the prior tool, but effective nonetheless. Here is a sample output:
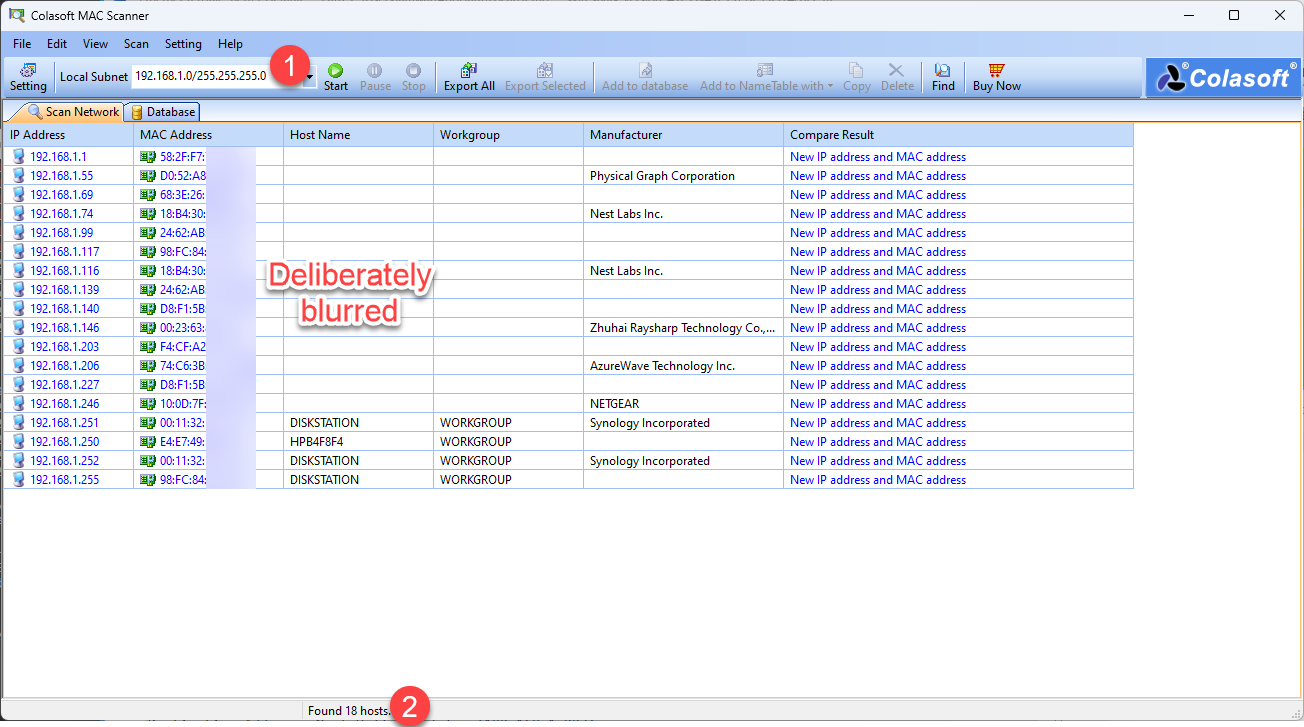
You can see that the results are not exactly the same because it only scanned one subnet (1). In this case it found 18 hosts (2).
There are few options as they have implemented more in the pay version. That said, I am not displeased.
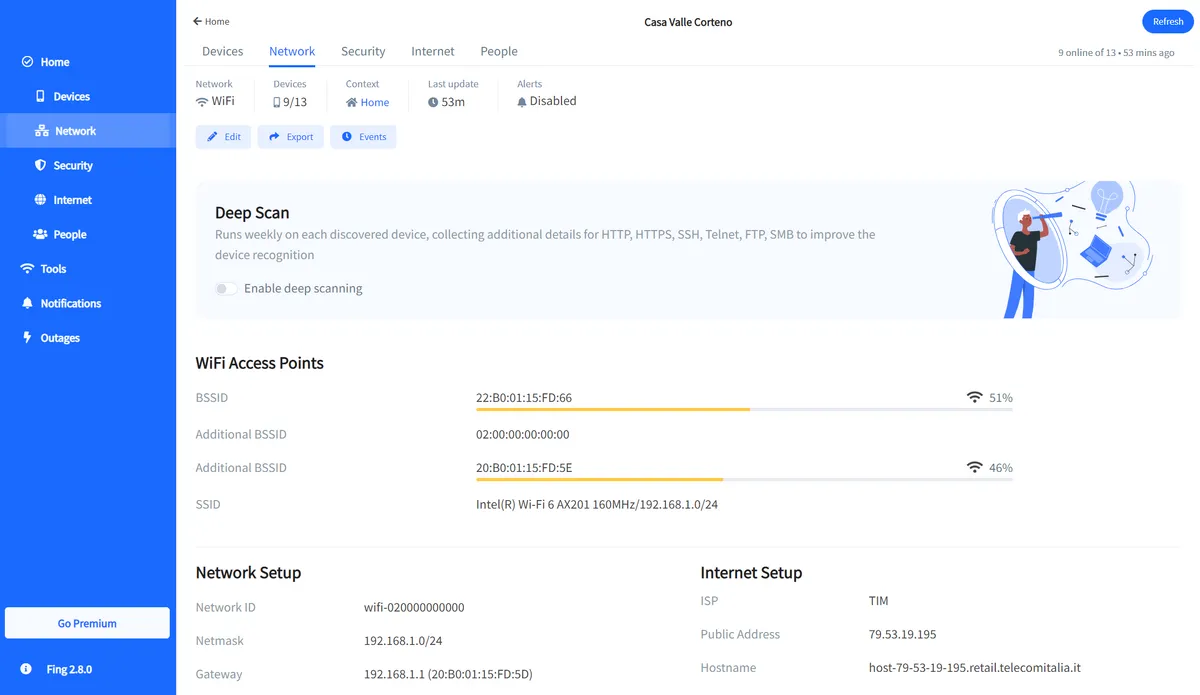
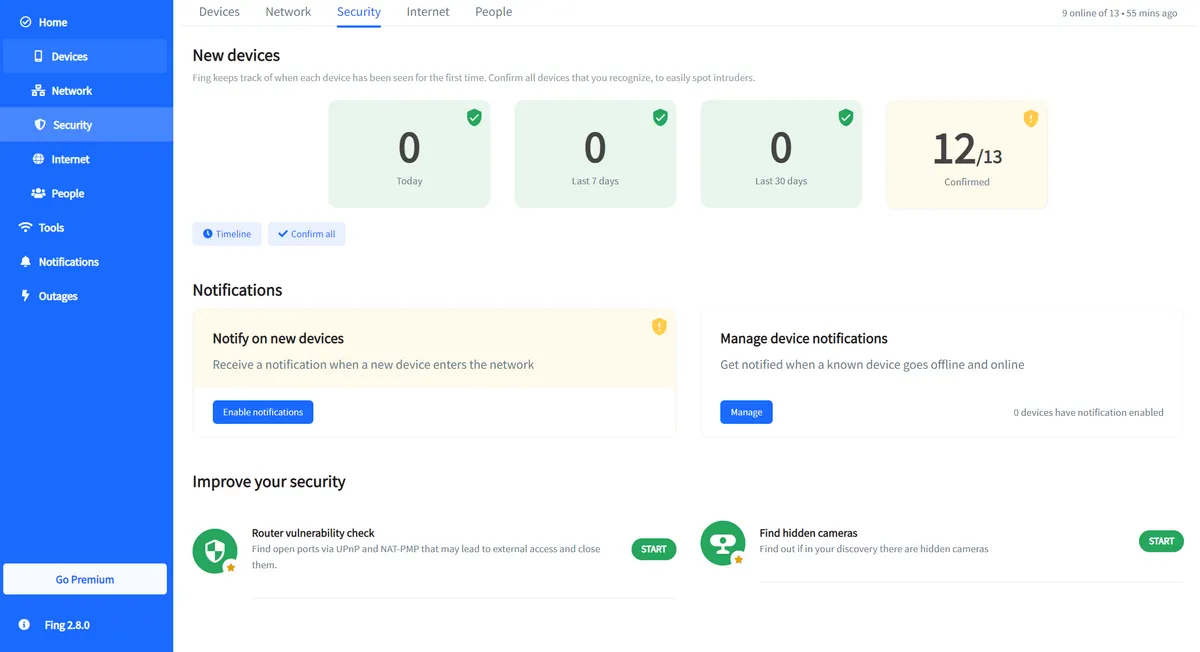
Fing
Fing is a pretty powerful network scanner and reporting tool that costs money for all the features. You will find this tool here: https://www.fing.com/products/fing-app
Here are a couple of screen shots from their web site:
Wireless Network Watcher
Yet another great free Windows tool from the folks at NirSoft is Wireless Network Watcher. While this tool has many features, watching for and detecting connected devices is one of them. You can find the tool here: https://www.nirsoft.net/utils/wireless_network_watcher.html
Here is an example of the output:
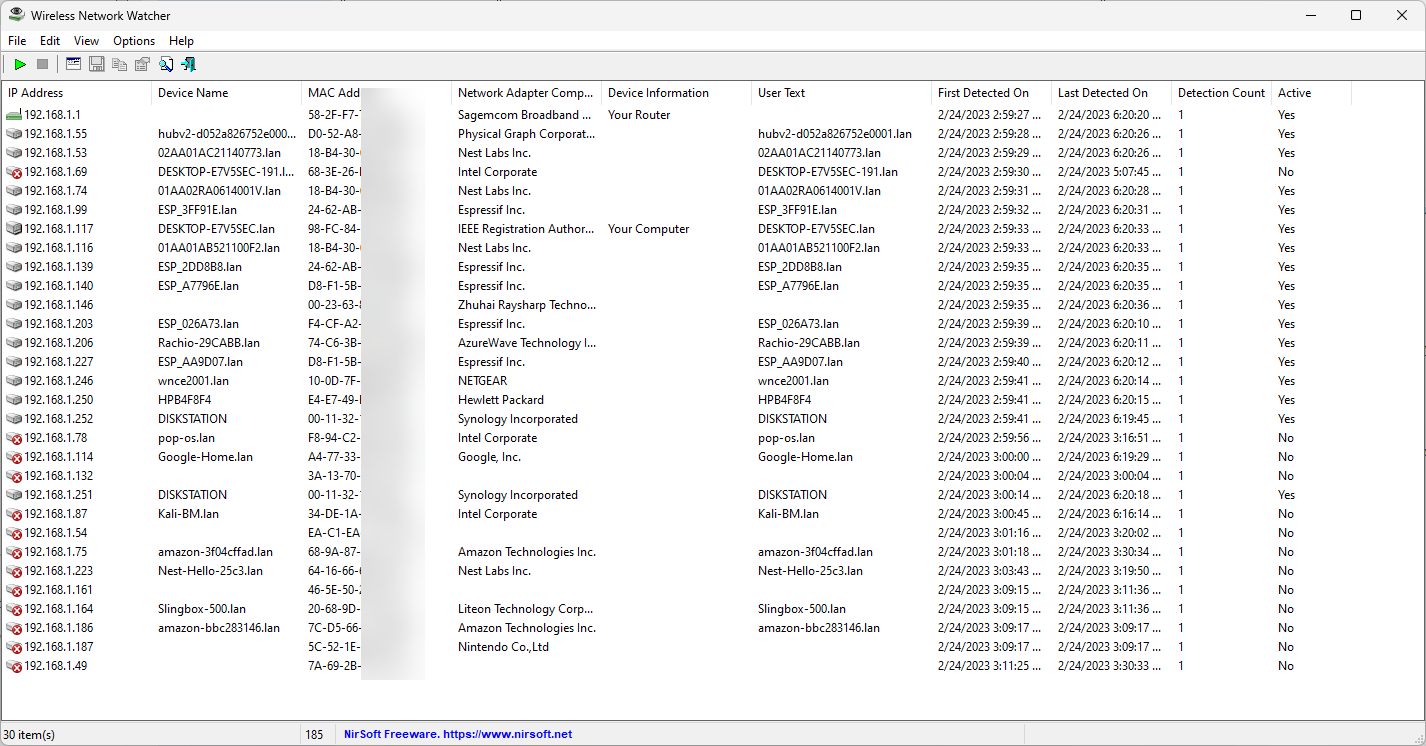
As with Advanced IP Scanner we get a list of devices, although we do not see expandable details available. What I find is the longer you leave this tool active, the more it finds – especially those pesky wireless devices that tend to go to sleep a lot. The scan above is once again my network, and you can tell it found more stuff.
Now they make a bunch of other tools that we will not cover here, including a tool called WakeMeonLAN – but I was not able to get it to trigger wireless devices that were asleep. The scanner above seemed to do just fine.
I hope you find this article and its content helpful.
Comments are welcomed below from registered users. You can also leave comments at our Discord server.
If you would like to see more content and articles like this, please support us by clicking the patron link where you will receive free bonus access to courses and more, or simply buying us a cup of coffee!
