Check out these additional IPv6 Resources: |
| Our IPv6 overview course at Udemy |
| Our IPv6 Custom Profiles for Wireshark |
| Our IPv6 classes at the Online School |
It should be no surprise to anyone reading this article that the next generation IPv6 protocol is being exploited by hackers and attackers just like its predecessor IPv4. If you have taken any of our general IPv6 courses, and especially our IPv6 Security course itself, you know we discuss the potential security vulnerabilities as well as some of the preventative measures that network designers/managers can and must take to minimize their exposure.
 First and foremost, everyone must understand clearly that IPv6 shares many security vulnerabilities with IPv4. There have been many reports and tests that suggest some IPv6 networks automatically drop any IPv6 packet that has extension headers due to vulnerabilities found when using IPv6 extension headers. Just because IPv6 has IPsec offered in extension headers does not prevent IPv6 from suffering the same security vulnerabilities in, for example, Application Layer attacks, Malware, Click-jacking, or Spyware. That said, there are other areas network administrators need to watch out for.
First and foremost, everyone must understand clearly that IPv6 shares many security vulnerabilities with IPv4. There have been many reports and tests that suggest some IPv6 networks automatically drop any IPv6 packet that has extension headers due to vulnerabilities found when using IPv6 extension headers. Just because IPv6 has IPsec offered in extension headers does not prevent IPv6 from suffering the same security vulnerabilities in, for example, Application Layer attacks, Malware, Click-jacking, or Spyware. That said, there are other areas network administrators need to watch out for.
So where are the additional weaknesses? The answer is that, based on the security trends as of the writing of this article, the weaknesses are in several areas. What we will do in this article is to discuss some of these vulnerabilities so that the reader can be more aware of what to tackle as they venture into IPv6.
Let’s begin with the dangers of IPv6 Tunnels. For example, Teredo and ISATAP tunnels are easily enabled if you have administrator privileges in the latest Windows versions such as Windows 7. That said, most all Windows versions since XP Service Pack 1 have easily supported IPv6. You can read more on how to disable IPv6 tunnel operations here.
Furthermore, any of the Linux distributions can have IPv6 easily enabled without a reboot, or have it enabled by default. These Operating Systems support both IPv4 and IPv6 in what we call “dual stack”. Click here, or here for Linux, or here for MAC, or here for Windows to see just how easy it is to enable and use IPv6 features.
Imagine a user that reads a little on IPv6 and finds out they can set up one of these IPv6 tunnels out of their corporate or school network. The result could be that their IPv6 tunnel will allow them to bypass IPv4 security policies and firewall rules as these systems usually aren’t configured to be IPv6 aware. Quite an incentive! With the firewall bypassed and security policies essentially disabled for their traffic, is that user’s IPv6 tunnel secure? Probably not. What they have inadvertently created is an IPv6 “island” inside their network while still having full IPv4 connectivity. If an intruder can access their tunnel from the Internet end, they can penetrate their machine and now have access into the corporate network from the inside. This IPv6 island has become an entrance point to the IPv4 network behind the firewall. Assuming the intruder is successful, they can now capture information on the IPv4 network and shuttle that traffic out of the corporate cloud via the IPv6 tunnel that is unguarded and unwatched by all the tools normally deployed.
Users are finding that, with the near invisibility of IPv6 traffic in tunnels off their corporate networks, Quality of Service policies tuned to control IPv4 packet streams are as unaware of IPv6 as the firewalls. So it is easy for a user to download and install an IPv6 application and bypass any Quality of Service rules such as congestion control or throttling. With wide open access, uploading or downloading video and other bandwidth hungry files is easy with tools like µTorrent, Bitflu, BitTornado, BitTorrent 6, Bits on Wheels, Deluge, KTorrent, Opera, qBittorrent, TorrentFlux, Tribler, Vuze (formerly Azureus), TorrentVolve and BitTyrant (all of these are IPv6 torrent apps). So if your voice over IP network is suffering from performance issues, it could be caused by the IPv6 traffic consuming bandwidth, and there is absolutely nothing in the QoS settings controlling that traffic. From a security standpoint, this is another problem that can be exploited to the point where denial of service to IPv4 traffic can occur.
The same issue applies to Internet Service Providers with regards to tunnels bypassing IPv4 controls and protection. For example, if the ISP is using controls for torrent traffic in IPv4, users who tunnel out of their locations through the ISP off to an IPv6 tunnel broker can run IPv6 torrent programs mentioned above essentially disabling the ISP torrent protection, again consuming bandwidth and leaving the ISP scratching their heads and wondering why their attempts to control the traffic are failing. Bring on the Wireshark! And you will need some IPv6 Wireshark profiles! Don’t worry, we have them here.
There are many other areas of concern for the Network Administrator and Service Providers beyond the tunneling problems. In December of 2007 the IETF RFC 5095 warned about a weakness in IPv6 that surrounds the Type 0 Routing Header (a feature that allows network administrators to identify IPv6 routers along a given data path). The IETF suggested that this capability be disabled by default as it could be used to instigate Denial of Service attacks. Most router manufacturers immediately modified their default settings. That said, by 2007 IPv6 had been around for many years and the in service devices did not have this protection. There are still reports of this issue being exploited, though most administrators have switched the feature off.
Security of an IPv6 network must be planned from the initial availability and turn up on any network. Since link local addresses are automatically created by IPv6 machines and network discovery can be allowed to be stateless, inadvertent users can easily join an IPv6 network and get a network address from a router, instead of the DHCP process like IPv4, and start communicating. Once in, it is a simple process to initiate any number of attacks, from virus dissemination to attempting to take over the network by emulating a router. If the attacker can emulate a router, they can issue Router Advertisements that tell all the users not to listen to the correct router and change addresses or cause the entire network to stop operating. In fact, the IETF has issued RFC 6105 to implement something called “RA Guard” which attempts to guard against these rogue router advertisements by authorizing which router is the real and correct router issuing the messages and directions. A new draft document from the IETF recently points out some flaws in the initial RA Guard specification, so the work continues in this area. This “Man in the Middle” operation must be prevented, especially with wireless networks that can be compromised by out of sight of security cameras.
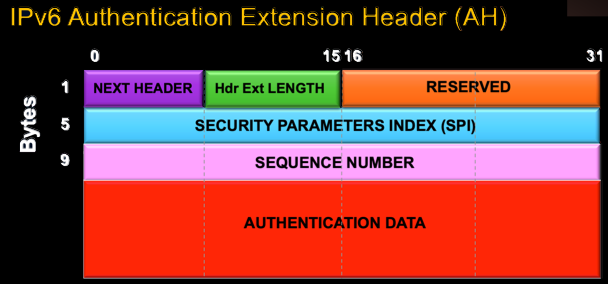
Other security threats are being analyzed, from Routing extension header problems to DNS query and advertisement weaknesses. So what is the bottom line? As of the writing of this article, every network administrator and service provider must implement IPv6 security measures as swiftly as possible. Upgrading firewalls, router configurations, and policies are vital to maintaining secure networking practices with IPv6. While security such as IPsec was designed into IPv6 from the start, the items identified in this article and the ones we will add as time marches forward (so stay tuned) require vigilance and engineering to minimize IPv6 network weaknesses.

