|
Check out these great references as well: |
| Our custom profiles repository for Wireshark |
| Our Udemy course on Wireshark |
| Our Udemy course on Wireless Packet capture |
Just introduced this week is a terminal version of tshark that looks like the Wireshark GUI call termshark.
Why?
Let’s say you run either Virtual Machines or Servers without a graphical user interface (GUI) and you want to do packet capture and analysis. The way we have done this is to run tcpdump or dumpcap or tshark from the command line (you can find our articles on tshark usage here), create .cap or .pcap files then offload them to a PC where we can use the Wireshark GUI to study the captures. With the new termshark tool, you can do similar analysis via SSH without a GUI. Now we say similar, because in the introduction we do not have all the features, nor is termshark a replacement for every function of the Wireshark GUI. Nonetheless, it is a superb start!
We wanted to try it right away. If you do also, here is how you get started on your Linux machine.
A note up front: there are critical dependencies for the installation to work, so be carefull not to go down the path we did which was a) clone the github repository, and b) try to run termshark. It won’t.
Frankly, the installation instructions on github are lacking at best, but I understand they have to be somewhat vague to avoid particular install issues.
Here is what I had to do on my Ubuntu Linux machine:
Step 1
Go to the github repository: https://github.com/gcla/termshark
Here is what the github site says:
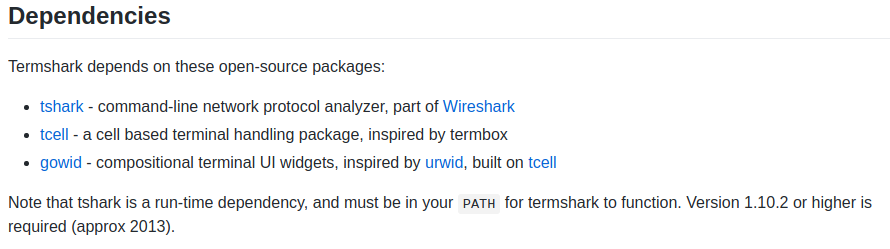
I had to install all these on my Linux machine that has Wireshark.
sudo apt install tshark
git clone https://github.com/gdamore/tcell.git
git clone https://github.com/gcla/gowid.git
Step 2
Now, the installation instructions say you must have the ‘go’ language installed, but no further details.
I did this with:
sudo apt install golang-go
Step 3
Now we can install termshark with the following command:
go get github.com/gcla/termshark/cmd/termshark
Step 4
We now need to add the following to the PATH:
PATH=$PATH:~/go/bin/
Step 5
If all is well, you should be able to run termshark. I was anxious and typed:
termshark
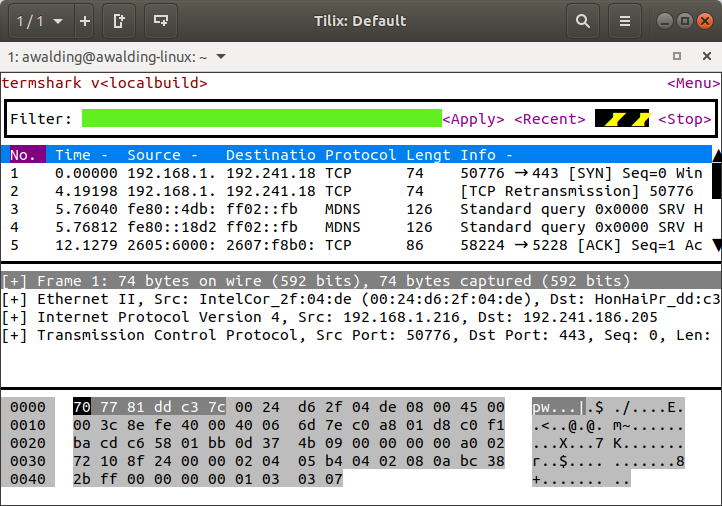
My system defaulted to the only interface I had active.
You may want to be more specific (to see your interfaces you can type ‘ip a’ or ‘ifconfig’ or ‘iwconfig’):
termshark -i {interface name}
Here is the ‘termshark -h’:
termshark v
A wireshark-inspired terminal user interface for tshark. Analyze network traffic interactively from your terminal.
See https://github.com/gcla/termshark for more information.
Usage:
termshark [FilterOrFile]
Application Options:
-i= Interface to read.
-r= Pcap file to read.
-d===, Specify dissection of
layer type.
-Y= Apply display filter.
-f= Apply capture filter.
–pass-thru=[yes|no|auto|true|false] Run tshark instead
(auto => if stdout is
not a tty). (default:
auto)
–log-tty=[yes|no|true|false] Log to the terminal..
(default: false)
-h, –help Show this help
message.
-v, –version Show version
information.
Arguments:
FilterOrFile: Filter (capture for
iface, display for
pcap), or pcap file
to read.
If –pass-thru is true (or auto, and stdout is not a tty), tshark will be
executed with the supplied command- line flags. You can provide
tshark-specific flags and they will be passed through to tshark (-n, -d, -T,
etc). For example:
$ termshark -r file.pcap -T psml -n | less
Something Cool
Here I am using SCAPY and watching the results in termshark, I use Tilix to create the multiple terminal windows:
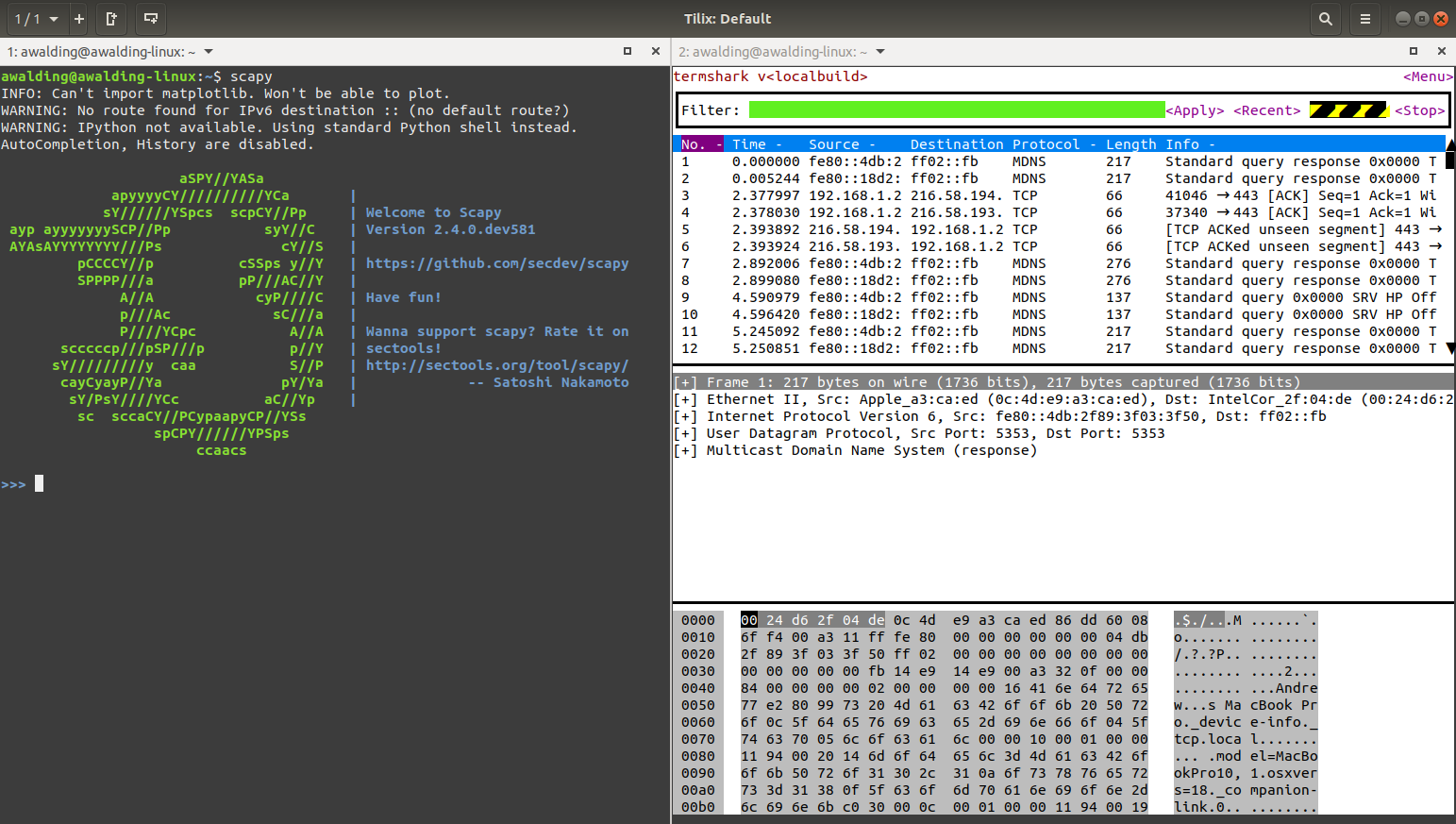
Oh yes!
Some usage examples:
| Command | Result |
| termshark -i wlo1 | Capture packets on the Wi-Fi interface |
| termshark -i eth0 | Capture packets on the Ethernet interface |
| termshark -i eth0 -f ip6 | Capture IPv6 packets on the Ethernet interface using the ‘ip6’ capture filter (you can simply replace ‘ip6’ with any valid BPF syntax) |
| termshark -r example.pcapng | Open the ‘example.pcapng’ capture file in termshark |
| termshark -r example.pcapng -Y ipv6 | Open the ‘example.pcapng’ capture file in termshark and apply the ‘ipv6’ display filter (you can simply replace ‘ipv6’ with any valid Wireshark display filter syntax) |
Hope this helps you get started with termshark.
Off to put this on some of my Linux non-GUI servers…..![]()
Comments are welcomed below from registered users. You can also leave comments at our Discord server.
If you would like to see more content and articles like this, please support us by clicking the patron link where you will receive free bonus access to courses and more, or simply buying us a cup of coffee!
