Many of our MPLS students and colleagues ask us about VRF Lite. The common question is “Can I use VRF Lite to simplify MPLS configuration?” The answer is, that VRF Lite actually has nothing to do with MPLS nor MPLS L3VPN per se. Let’s define what VRF Lite is. A VRF is a Virtual Routing and Forwarding instance, meaning a separate routing table from the global routing table in a router. By creating a VRF and associating it with an interface, you can seperate routing on that interface from the global routing table, creating different control plane environments. It’s like creating a little virtual router inside the router itself. The benefit of doing this is you can create separation of traffic and separation of control of traffic at Layer 3 in a similar way that VLAN’s separate traffic in Layer 2.
Let’s take a look at a basic network configuration:
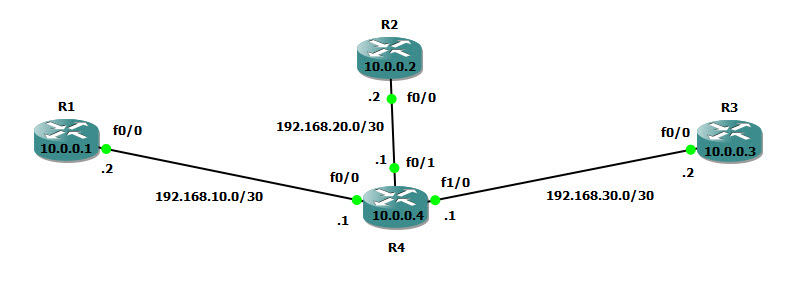
We begin with a normal routed network where all the routers R1, R2, R3 and R4 can see each other. Here is the routing table in R4:
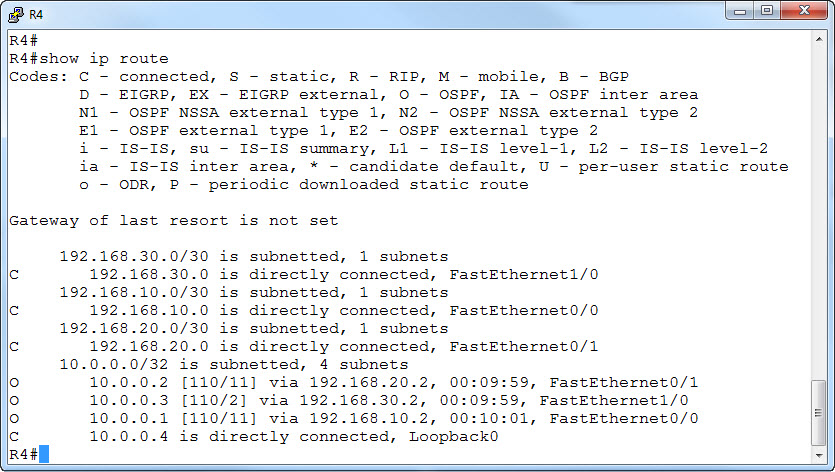
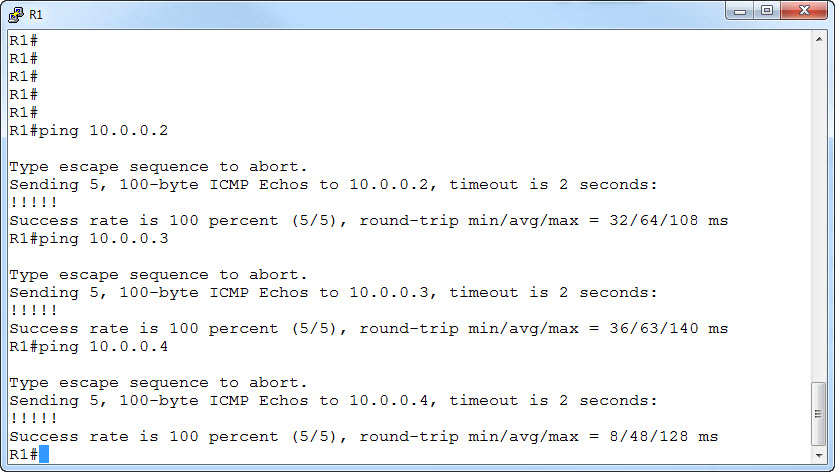
And we can ping between the routers (note that I have selected R1 and ping each of the other three routers):
Now, to demonstrate VRF Lite, let’s say I want to separate R1 and R2 into a separate control plane, while leaving R3 in the global routing table of R4. This would mean that from R1, I should only be able to ping R2 and vice versa.
We start by creating a VRF for the R1 and R2 routers to use on R4. We will call it VPN-R1R2.
R4#configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
R4(config)#ip vrf VPN-R1R2
R4(config-vrf)#
You can see we are now in configuration mode of the VRF.
Next we want to apply this VRF to the two interfaces on R4 that are connected to R1 and R2 respectively. Let’s start with the interface to R1 which is f0/0:
R4(config-vrf)#interface f0/0
To associate the VRF with this interface enter:
R4(config-if)#ip vrf forwarding VPN-R1R2
You will get two errors from the router:
% Interface FastEthernet0/0 IP address 192.168.10.1 removed due to enabling VRF VPN-R1R2
R4(config-if)#
*Mar 1 00:21:05.083: %OSPF-5-ADJCHG: Process 1, Nbr 10.0.0.1 on FastEthernet0/0 from FULL to DOWN, Neighbor Down: Interface down or detached
R4(config-if)#
The first error is that IOS will remove the IP address from the interface. That is because the interface is removed from the global routing table. We will need to re-install the address, and then it will appear in the vrf.
The second error, was that with the VRF now in place, the OSPF adjacency is broken, and this is exactly what we wanted!
We need to fix the IP address first:
R4(config-if)#ip address 192.168.10.1 255.255.255.252
Now lets go to the interface facing R2 and do the same thing:
R4(config-if)#interface f0/1
R4(config-if)#ip vrf forwarding VPN-R1R2
% Interface FastEthernet0/1 IP address 192.168.20.1 removed due to enabling VRF VPN-R1R2
R4(config-if)#
*Mar 1 00:27:57.371: %OSPF-5-ADJCHG: Process 1, Nbr 10.0.0.2 on FastEthernet0/1 from FULL to DOWN, Neighbor Down: Interface down or detached
R4(config-if)#ip address 192.168.20.1 255.255.255.252
R4(config-if)#end
Now let’s do a show command to verify the VRF is installed properly:
R4#show ip vrf
Name Default RD Interfaces
VPN-R1R2 <not set> Fa0/0
Fa0/1
R4#
Note that we have no Route Distinguisher (RD) as we are not doing MPLS!
We can also look at the routing of the VRF and global table and see that the interfaces are no longer in the global routing:
R4#show ip route
Codes: C – connected, S – static, R – RIP, M – mobile, B – BGP
D – EIGRP, EX – EIGRP external, O – OSPF, IA – OSPF inter area
N1 – OSPF NSSA external type 1, N2 – OSPF NSSA external type 2
E1 – OSPF external type 1, E2 – OSPF external type 2
i – IS-IS, su – IS-IS summary, L1 – IS-IS level-1, L2 – IS-IS level-2
ia – IS-IS inter area, * – candidate default, U – per-user static route
o – ODR, P – periodic downloaded static route
Gateway of last resort is not set
192.168.30.0/30 is subnetted, 1 subnets
C 192.168.30.0 is directly connected, FastEthernet1/0
10.0.0.0/32 is subnetted, 2 subnets
O 10.0.0.3 [110/2] via 192.168.30.2, 00:03:43, FastEthernet1/0
C 10.0.0.4 is directly connected, Loopback0
To look at the VRF:
R4#show ip route vrf VPN-R1R2
Routing Table: VPN-R1R2
Codes: C – connected, S – static, R – RIP, M – mobile, B – BGP
D – EIGRP, EX – EIGRP external, O – OSPF, IA – OSPF inter area
N1 – OSPF NSSA external type 1, N2 – OSPF NSSA external type 2
E1 – OSPF external type 1, E2 – OSPF external type 2
i – IS-IS, su – IS-IS summary, L1 – IS-IS level-1, L2 – IS-IS level-2
ia – IS-IS inter area, * – candidate default, U – per-user static route
o – ODR, P – periodic downloaded static route
Gateway of last resort is not set
192.168.10.0/30 is subnetted, 1 subnets
C 192.168.10.0 is directly connected, FastEthernet0/0
192.168.20.0/30 is subnetted, 1 subnets
C 192.168.20.0 is directly connected, FastEthernet0/1
That was great! However R1 and R2 cannot see each other. So we have to add a separate OSPF instance (we will call it OSPF 2) for the VRF routing on R4 as follows:
R4#configure terminal
Enter configuration commands, one per line. End with CNTL/Z.
R4(config)#router ospf 2 vrf VPN-R1R2
R4(config-router)#network 192.168.20.0 0.0.0.3 area 1
R4(config-router)#network 192.168.10.0 0.0.0.3 area 1
You should see both routing adjacencies come up:
*Mar 1 00:36:40.139: %OSPF-5-ADJCHG: Process 2, Nbr 10.0.0.2 on FastEthernet0/1 from LOADING to FULL, Loading Done
*Mar 1 00:36:47.947: %OSPF-5-ADJCHG: Process 2, Nbr 10.0.0.1 on FastEthernet0/0 from LOADING to FULL, Loading Done
Perfect. So let’s look again at the VRF routing:
R4#show ip route vrf VPN-R1R2
Routing Table: VPN-R1R2
Codes: C – connected, S – static, R – RIP, M – mobile, B – BGP
D – EIGRP, EX – EIGRP external, O – OSPF, IA – OSPF inter area
N1 – OSPF NSSA external type 1, N2 – OSPF NSSA external type 2
E1 – OSPF external type 1, E2 – OSPF external type 2
i – IS-IS, su – IS-IS summary, L1 – IS-IS level-1, L2 – IS-IS level-2
ia – IS-IS inter area, * – candidate default, U – per-user static route
o – ODR, P – periodic downloaded static route
Gateway of last resort is not set
192.168.10.0/30 is subnetted, 1 subnets
C 192.168.10.0 is directly connected, FastEthernet0/0
192.168.20.0/30 is subnetted, 1 subnets
C 192.168.20.0 is directly connected, FastEthernet0/1
10.0.0.0/32 is subnetted, 2 subnets
O 10.0.0.2 [110/11] via 192.168.20.2, 00:03:25, FastEthernet0/1
O 10.0.0.1 [110/11] via 192.168.10.2, 00:03:25, FastEthernet0/0
We see the routes have been learned.
Now let’s see if R1 and R2 can see each other:
R1#ping 10.0.0.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.0.0.2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 48/72/152 ms
But, we should not be able to ping to R3:
R1#ping 10.0.0.3
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.0.0.3, timeout is 2 seconds:
…..
Success rate is 0 percent (0/5)
Perfect!
One side note: R4 cannot ping R1 and R2 either, but it can see R3:
R4#ping 10.0.0.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.0.0.1, timeout is 2 seconds:
…..
Success rate is 0 percent (0/5)
R4#ping 10.0.0.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.0.0.2, timeout is 2 seconds:
…..
Success rate is 0 percent (0/5)
R4#ping 10.0.0.3
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.0.0.3, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 20/55/88 ms
So the way we do this is specify the ping via the VRF:
R4#ping vrf VPN-R1R2 10.0.0.1
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.0.0.1, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 12/48/104 ms
R4#ping vrf VPN-R1R2 10.0.0.2
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.0.0.2, timeout is 2 seconds:
!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 20/65/124 ms
And therefore we cannot see R3 this way:
R4#ping vrf VPN-R1R2 10.0.0.3
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 10.0.0.3, timeout is 2 seconds:
…..
Success rate is 0 percent (0/5)
We hope this helps you understand VRF Lite.

