Too many people shrug off Linux for fears of security with a free and open source operating system, even today. For those of us who know that Linux is no less or more secure than any other operating system, we must be sensitive to this and we must be well versed in Linux commands that relate to the secure operation of the Linux OS. Now there are so many variants, so I won’t dive into this, instead a will take a high road and the reader should understand these commands should apply to most Linux distributions, though I encourage comments below for either something I left out, or something that other readers need to know with various distribution differences.
For reference, I am running Ubuntu in my examples below. Lastly, be sure to look at any new commands I may cover below by using the ‘man’ command. With all that said, let’s dive in.
The Proper Secure Implementation of ‘sudo’
For me, this is an important starting point. As most Linux users have found out, dangerous commands are “privileged” commands in the Linux environment. The root user has access to all commands and will not run into any issues. This raises a critical security issue that must be properly deployed. The industry recommends that you not default to using the root user. Instead use a “normal” user and depend on the sudo command to execute those potentially dangerous commands. Furthermore, in multi-user systems, some users will not receive super user privileges.
Access to the sudo commands and privileges is tracked in the /etc/sudoers and /etc/group files. Let’s have a look at my /etc/sudoers file (yours may look different):
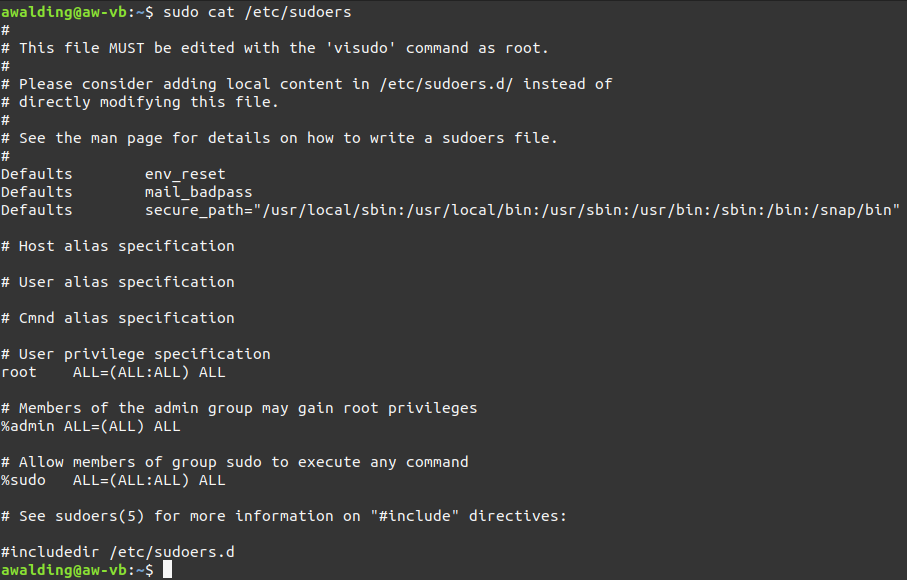
Notice, the system says to use visudo to make changes to this file. The sudo privileges can be assigned by user or by group. Most Linux systems, like mine above, the /etc/sudoers file will already be configured with groups (mine has the admin group preceded with a %) that allow the privileges to be assigned to groups set up in the /etc/group file. So if you assign a user to the admin group on my system they will gat sudo privileges and you do not need to edit the /etc/sudoers file.
One other note on visudo. Use the “sudo update-alternatives – config editor” command if you don’t like the default editor that’s called into play when you run the visudo command. It will offer a number of editors as options and change your setting.
Keep in mind, the whole point of this is to limit user access to the
The simplest way to give someone sudo privileges is to add them to the admin group in /etc/group. The problem with this approach is that they can run any command as root. If you want some users to have root authority for a limited set of commands (e.g., adding and removing accounts) you can define the commands you want them to be able to run through a command alias like this:
Cmnd_Alias ACCT_CMDS = /usr/sbin/adduser, /usr/sbin/deluser
Then give the user or group the ability to run these commands using sudo with a command like one of these:
fred ALL=(ALL) ACCT_CMDS
%support ALL=(ALL:ALL) ACCT_CMDS
The first line allows the user “fred” to run the twp (adduser and deluser) commands with sudo. The second command assigns the same privileges to anyone in the “support” group in the /etc/group file.
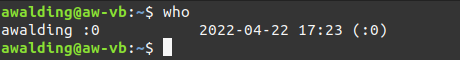
The w and who Commands
The w and who commands show you who is logged into the system. The w command shows more information such as where they logged in from, when they logged in and how long they’ve been idle. Here is and example of the w command:

By comparison, here is an example of the who command:
By the way, you can read more on creating users in my article here: https://www.cellstream.com/reference-reading/tipsandtricks/582-using-the-useradd-command-to-create-user-accounts-in-linux
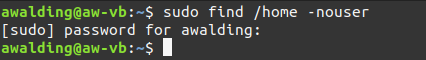
The find Command
When it comes to security, you might find yourself looking for files that have no owners (no corresponding accounts), or files that are both world-writable and executable. This is where the find command comes in handy. Find commands are easy to create but require some familiarity with the multitude of options for defining what you’re looking for.
Let’s start with finding files that have no currently defined owners:
awalding@aw-vb:~nbsp;sudo find /home -nouser
In my case, I show none. This is good:
Now, let’s find files that likely anyone can both run and modify. Warning: Before you do, this will likely scroll off the screen for quite a while. The -o in the command refers to the “other” group – not the owner and not the group associated with the files. My suggestion is to further modify this for your needs. Perhaps some readers will add examples in the comments of how to better use the find command.
awalding@aw-vb:~$ sudo find / -perm -o=wx
The file Command
The file command examines a file and determines what kind of file it is based on its contents, not its name. Many files (like jpeg files) contain identifiers near the beginnings of the files that identify them. Take a look at the example I found on the Internet. The “.jpg” file is clearly not a true jpeg file, instead it is an executable even though it has the .jpg file extension:
fred@linux:~$ file myphoto.jpg
myphoto.jpg: ELF 64-bit LSB executable, x86-64, version 1 (SYSV), dynamically linked, interpreter /lib64/ld-linux-x86-64.so.2, for GNU/Linux 3.2.0, BuildID[sha1]=5d19f7a492405ea9b022a9aa8151f6fb4143633d, stripped
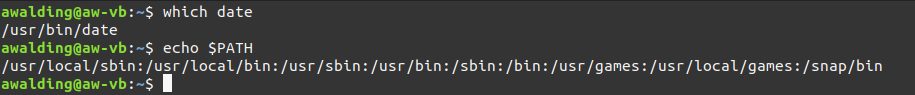
The which Command
The which command will help identify what executable will run when you type a command. On a compromised system, this won’t always be what you think it is. For example, if a Trojan has been inserted into the file system in a location that shows up in your search path before the legitimate one, it will be run instead. This is a good reason to ensure that your search path includes directories like /usr/bin before it adds less standard locations and especially before “.” (the current directory).
Here is a possible example. Let’s start with a known good system:

This is what we would expect when we type the ‘date’ command.
And for good measure – let’s look at this user’s $PATH:
But what is we got something different (now I am making this up for illustration purposes):
fred@aw-vb:~$ which date
/usr/local/bin/date
That is not good. We can check a user’s search path by switching to the user and echoing it:
awalding@aw-vb:~$ sudo su - fred
fred@aw-vb:~$ echo $PATH
/usr/local/bin:/usr/bin:/bin:/usr/local/games:/usr/games:/snap/bin
Even if users’ search paths are set up in a system file like /etc/profile or /etc/bash.bashrc, they may have been altered by local settings.
The last Command
The last command will display recent logins for users and is often helpful when you’re trying to track down changes or other activity.
The command syntax is:
awalding@aw-vb:~$ last {username}Here is an example:
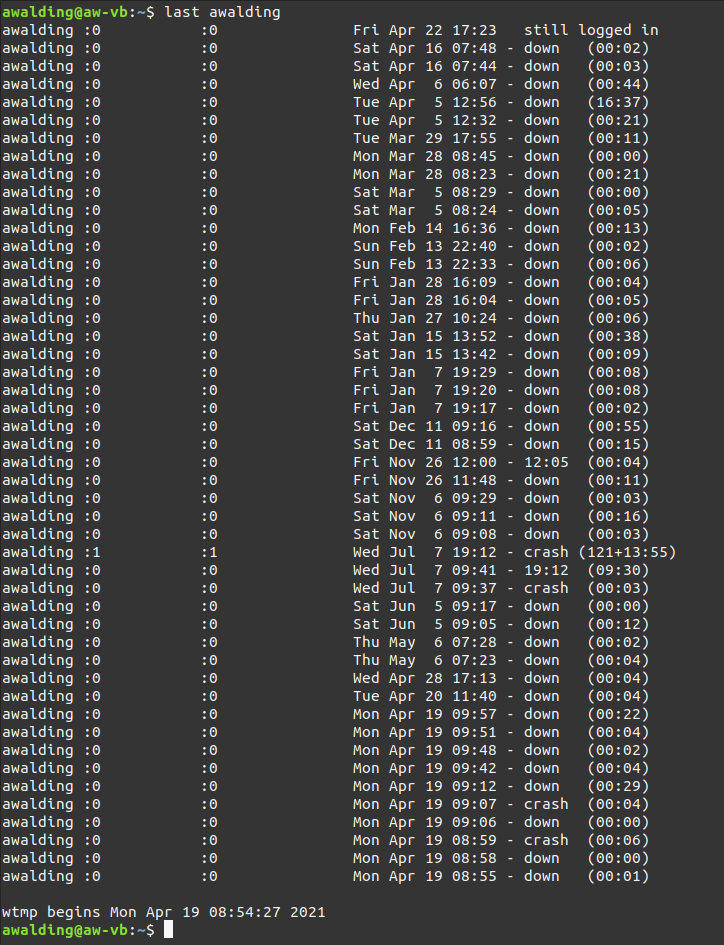
You can imagine that using this command as routine maintenance to find users that have not logged in in a long time or users that have logged in more that expected, or users that are always logged in.
The ss Command
The ss command is a tool for investigating network sockets that exist on the Linux system. Technically, a socket is the combination of Source IP Address and port number and Destination IP and port number. In Linux, when the ss command is run you get something like this (I am just showing the first several lines):
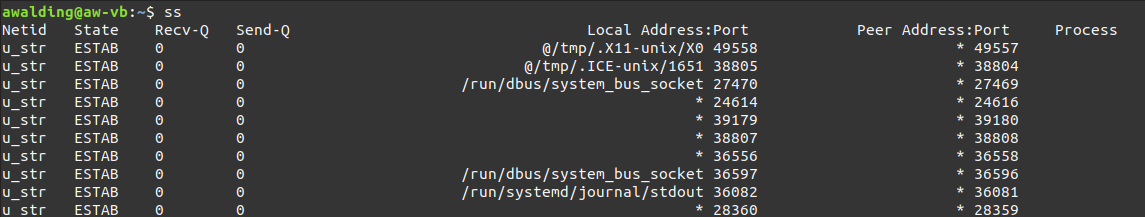
Notice the Local Address:port and the Peer Address:port – these are the sockets.
The ss command allows you to do things like display listening ports and active connections. As we see above, without adding some constraints, running ss with no command line options is going to display a lot more information than you probably want to look at. After all, many legitimate parts of the operating system communicate via these sockets. If you want to generate a list of established connections or listening ports (i.e., services available to external systems), more specific ss commands can prove very useful.
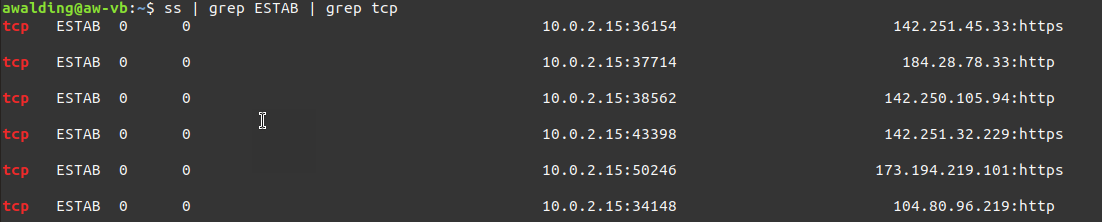
Looking at Established Connections
awalding@aw-vb:~$ ss -t

awalding@aw-vb:~$ ss | grep ESTAB | grep tcp
Looking at Ports that are Listening
awalding@aw-vb:~$ ss -ltn

Notice that port 631 (CUPS) is only listening on the loopback interface (127.0.0.1).
The iptables Commands
Firewall rules are important and you can see if there are any rules on your system by using the following commands:
awalding@aw-vb:~$ sudo iptables -vL -t filterawalding@aw-vb:~$ sudo iptables -vL -t natawalding@aw-vb:~$ sudo iptables -vL -t mangleawalding@aw-vb:~$ sudo iptables -vL -t rawawalding@aw-vb:~$ sudo iptables -vL -t security
My system did not have any, so do not be surprised if yours does not either. Should you have these rules in place is beyond the scope of this article.
The ip Command
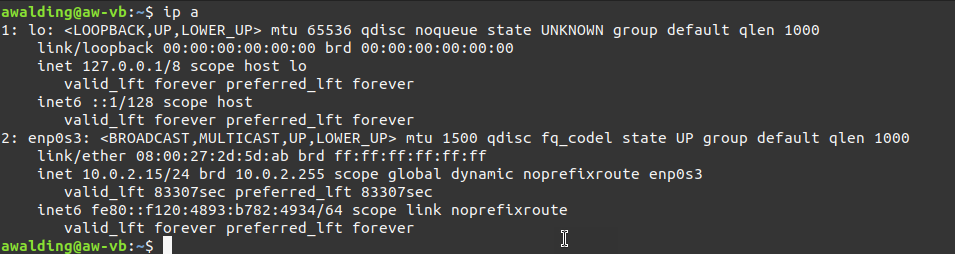
The ip command allows you to display information on your network interfaces on the Linux system. Here is mine:
The ip route Command
Am I going to the right default gateway? The ip route command will display your routing table:

The kill, pkill & killall Commands
All Linux systems offer a convenient selection of commands for terminating processes regardless of why you want them stopped. You can “kill” by the process ID or by the name of the process. Furthermore, you can kill individual processes or a groups of processes. You should be ready to use these process terminators. Here are a few examples:
awalding@aw-vb:~$ kill {process #}awalding@aw-vb:~$ pkill {process name}awalding@aw-vb:~$ killall {group}
The passwd Command
We would all agree that the passwd command is probably an obvious security related command and it should not be omitted from any Linus security command list. Having a well thought out and proper policy for password changes, especially as users come and go, and user roles change, is extremely important. That said, the passwd command isn’t just used to change passwords, however. You can also use it with sudo privilege to change other users’ passwords, lock/unlock or expire accounts, check account status and change the settings that determine when a password expires or time password warnings.
Check the man page (man passwd) for details and use commands like these:
awalding@aw-vb:~$ sudo passwd {username} -----> change {username}'s passwordawalding@aw-vb:~$ sudo passwd -e {username} -----> expire {usernames}'s password (forces them to reset it)awalding@aw-vb:~$ sudo passwd -i {username} -----> disable {username}'s accountThe pwck Command
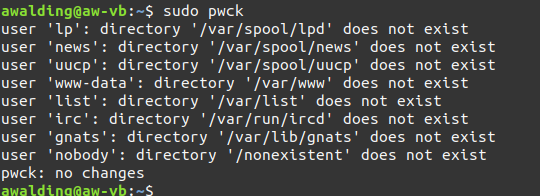
The pwck command does kind of a sanity check on your /etc/passwd and /etc/shadow files to make sure required fields are present, files and directories exist, and so forth. Some of these issues are expected, but a good system administrator will note issues, like users with no home that should have one. Here is my system, and none of these are issues:
Summing Up
In this article I took a little peek at some useful Linux commands to help you maintain security on a Linux system. Certainly this was not all encompassing and I am sure readers and visitors will have some additional commands they will suggest in comments. We all welcome those pearls of wisdom on this subject.
I hope you find this article and its content helpful. Comments are welcomed below. If you would like to see more articles like this, please support us by clicking the patron link where you will receive free bonus access to courses and more, or simply buying us a cup of coffee!, and all comments are welcome!